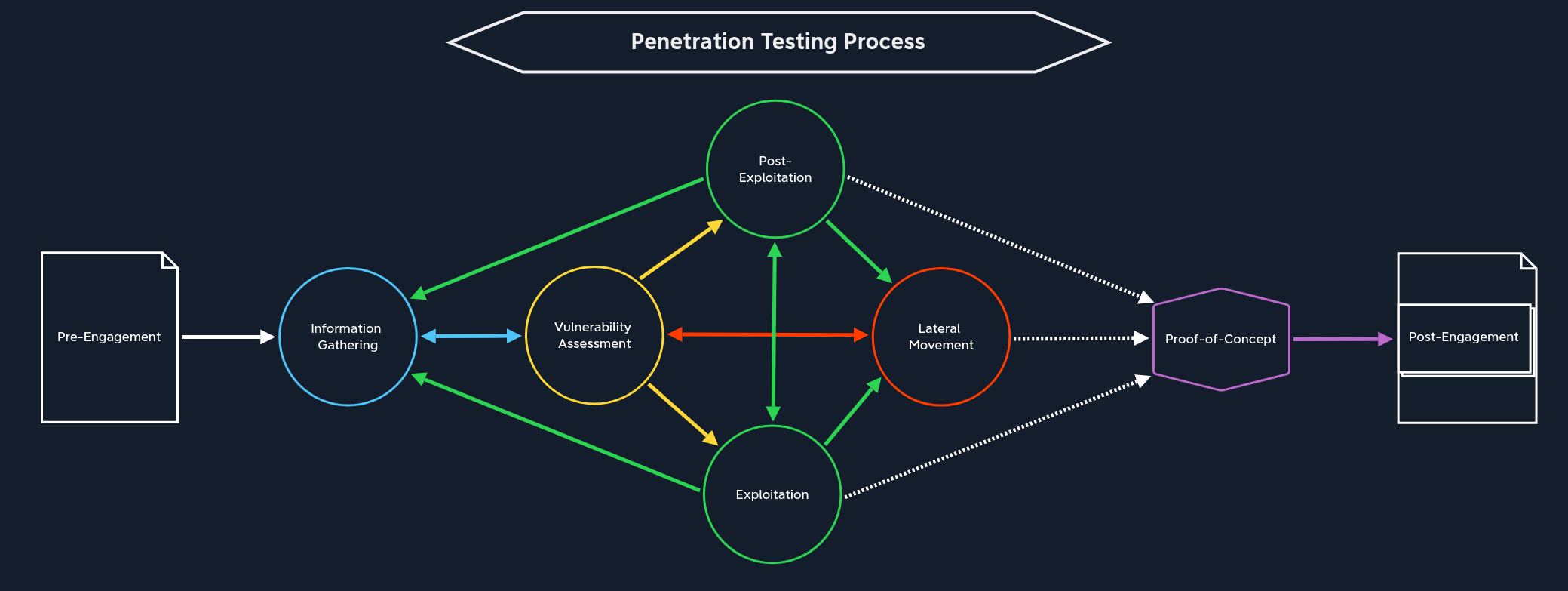
- Penetration Testing Process
- Estimated time: 6h
- Actual time: 2h
- Getting Started
- Estimated time: 8h
- Actual time: 5h
- Network Enumerated With Nmap
- Estimated time: 7h
- Actual time: 3h
- Footprinting
- Estimated time: 16h
- Actual time:
- Information Gathering - Web Edition
- Estimated time: 8h
- Actual time:
- Vulnerability Assessment
- Estimated time: 16h
- Actual time:
- File Transfers
- Estimated time: 3h
- Actual time:
- Transferring Files
- Shells & Payloads
- Using The Metaspoit Framework
- Estimated time: 5h
- Actual time:
- Password Attacks
- Estimated time: 8h
- Actual time:
- Attacking Common Services
- Estimated time: 8h
- Actual time:
- Pivoting, Tunneling, And Port Forwarding
- Estimated time: 16h
- Actual time:
- Active Directory Enumeration & Attacks
- Estimated time: 56h
- Actual time:
- Using Web Proxies
- Estimated time: 8h
- Actual time:
- Attacking Web Applications With Ffuf
- Estimated time: 5h
- Actual time:
- Login Brute Forcing
- Estimated time: 6h
- Actual time:
- SQL Injection Fundamentals
- Estimated time: 8h
- Actual time:
- SQLMap Essentials
- Estimated time: 8h
- Actual time:
- Cross-Site Scripting (XSS)
- Estimated time: 6h
- Actual time:
- File Inclusion
- Estimated time: 8h
- Actual time:
- File Upload Attacks
- Estimated time: 8h
- Actual time:
- Command Injections
- Estimated time: 6h
- Actual time:
- Web Attacks
- Estimated time: 16h
- Actual time:
- Attacking Common Applications
- Estimated time: 32h
- Actual time:
- Linux Privilege Escalation
- Estimated time: 8h
- Actual time:
- Windows Privilege Escalation
- Estimated time: 32h
- Actual time:
- Documentation & Reporting
- Estimated time: 16h
- Actual time:
- Attacking Enterprise Networks
- Estimated time: 16h
- Actual time: